IMath Lecture Series: Dr. Kiyoshi Nagata
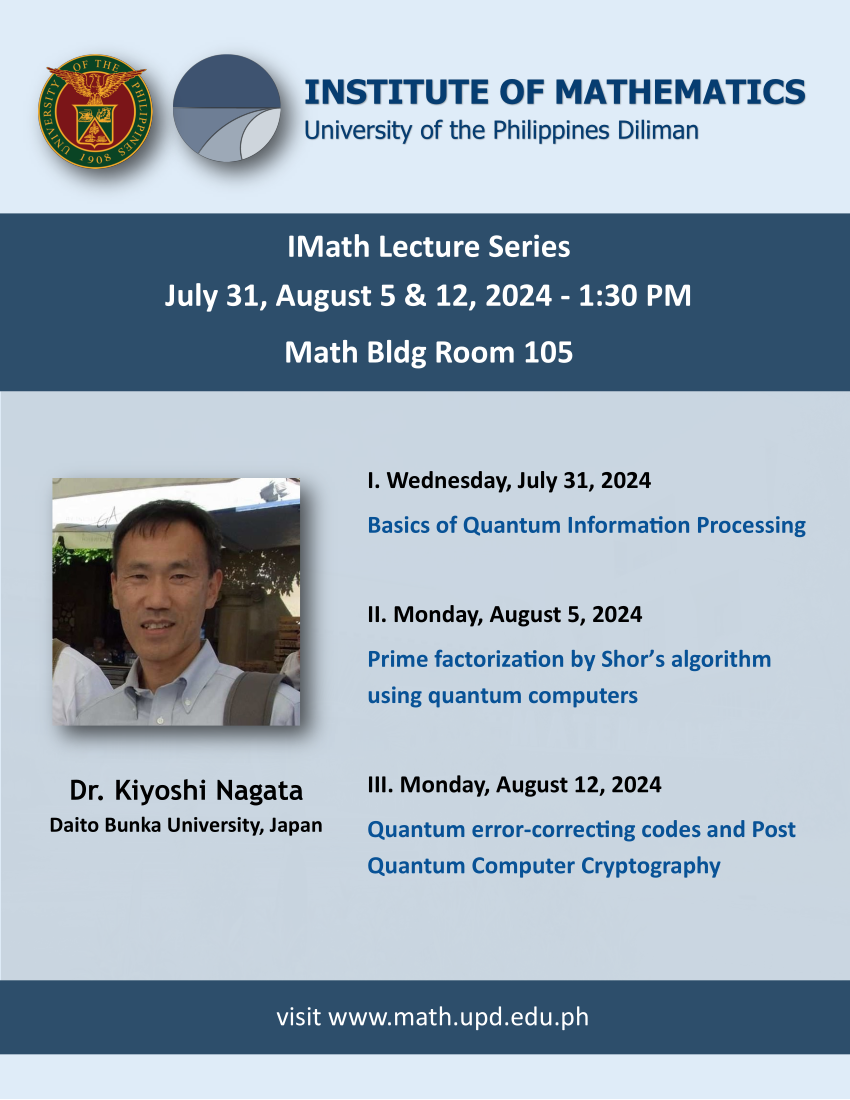
You are all invited to a series of lectures to be given by Dr. Kiyoshi Nagata, a visiting professor from the Faculty of Business Administration, Daito Bunka University, Tokyo, Japan. His talks will be held on July 31 (Wednesday), August 5 (Monday), and August 12 (Monday). All of his talks will start at 1:30 PM and will be held at the Institute of Mathematics Building, Room 105.
Lecture 1 (Wednesday, July 31): Basics of Quantum Information Processing
Abstract: The basic unit of information processing in quantum computers is the quantum bit, and several physical methods have been proposed, such as using photons or quantum spin. Here, we will not consider the physics, but will look at how quantum bits are mathematically represented and how they are transformed by basic quantum gates. The quantum Fourier transform and the axioms for quantum measurements will then be discussed.
Lecture 2 (Monday, August 5): Prime factorization by Shor’s algorithm using quantum computers
Abstract: The security of many public key cryptosystems, including the RSA public key cryptosystem, is based on the computational capabilities of classical computers, since the amount of calculation required to factor a large integer grows exponentially with the number of bits in the given integer. Even using the so-called number field sieve, the prime factorization requires quasi-exponential operations using classical computers. Some of typical methods for solving the prime factorization problem is reduced to the order-finding problem. Shor, in 1994, noticed that the quantum order-finding algorithm could reduced to the order-finding problem which can be solved in polynomial time.
Lecture 3 (Monday, August 12): Quantum error-correcting codes and Post Quantum Computer Cryptography
Abstract: In quantum information theory, the superposition state is maintained until an observation is made, at which point only one state is determined. Error-correction is one of important problems to which the stabilizer code can be applied. On the other hand, some public key cryptosystems based on the difficulty of the order-finding problem are under threat. Thus cryptosystems – called post quantum cryptosystems – which are difficult to decipher even using quantum computers are desired and studied. Among these, methods using error-correcting codes are one of the most promising candidates, and research is being conducted on them along with decoding methods using quantum computers.
